SU_Protocol-WriteUp
13k字 •
25分钟
前言
此题采取 Themida 静态压缩 + 动态修改密钥 + 预期多解的思路防止 ai 一把梭(被一些师傅骂 misc 了 😭
WP
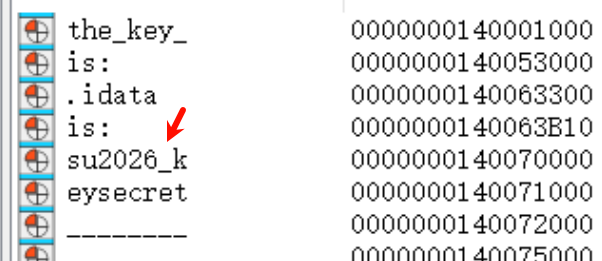
密钥写在段名中,预期解法是 x64dbg 运行时进行 dump,由于 Themida 的原因一定会查看段内存(下断点),所以人类选手(应该)能找到此 key
1 | su2026-keysecret |
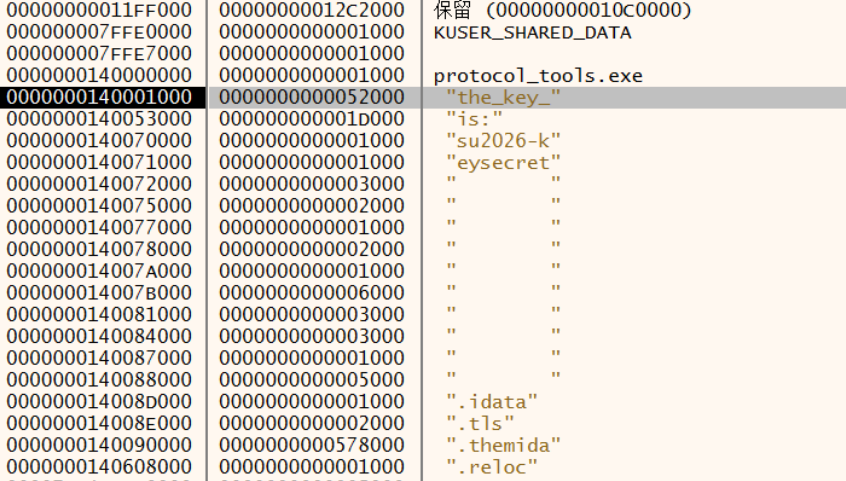
有个别师傅被 ida 坑了,见下图
流程
注册 /flag POST 路由来接收用户输入
整体字段(感谢 r3 的师傅图表做的这么好 :D)
1 | Offset Value Meaning |
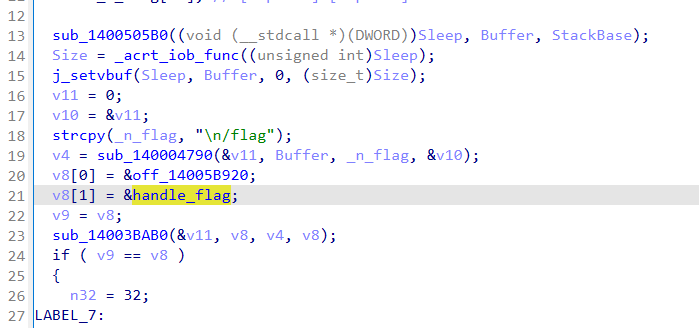
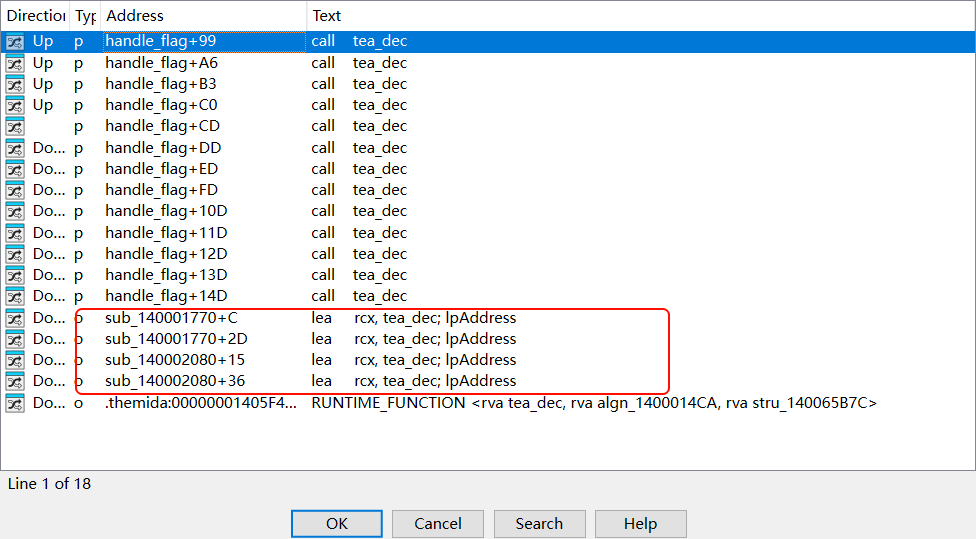
构造 payload (使用正确的 key 和 delta 进行 tea 加密)
1 | 802ba5e6806f7dd07b988241146e350f481ec220fe1536b67193671193ca08060fd065ddf9c197a119d2f732d8c574e7fc8ca862a2a15e3e7312df0fe81b0f810bf27f7f8982b9a1880ac3d3fd128acabe866e82655cb2b536edf8714ec03162c91ed2c534c132a3347375323032362d6b6579736563726574 |
构造整体
1 | 60 00 7c 80 55 00 <payload> 45 16 |
1 | 60007c805500802ba5e6806f7dd07b988241146e350f481ec220fe1536b67193671193ca08060fd065ddf9c197a119d2f732d8c574e7fc8ca862a2a15e3e7312df0fe81b0f810bf27f7f8982b9a1880ac3d3fd128acabe866e82655cb2b536edf8714ec03162c91ed2c534c132a3347375323032362d6b65797365637265744516 |
补上外层 # 和 \n 之后再做一次 hex string
1 | #60007c805500802ba5e6806f7dd07b988241146e350f481ec220fe1536b67193671193ca08060fd065ddf9c197a119d2f732d8c574e7fc8ca862a2a15e3e7312df0fe81b0f810bf27f7f8982b9a1880ac3d3fd128acabe866e82655cb2b536edf8714ec03162c91ed2c534c132a3347375323032362d6b65797365637265744516\x0a |
1 | 233630303037633830353530303830326261356536383036663764643037623938383234313134366533353066343831656332323066653135333662363731393336373131393363613038303630666430363564646639633139376131313964326637333264386335373465376663386361383632613261313565336537333132646630666538316230663831306266323766376638393832623961313838306163336433666431323861636162653836366538323635356362326235333665646638373134656330333136326339316564326335333463313332613333343733373533323330333233363264366236353739373336353633373236353734343531360a |
对该字符串做 md5 即为 flag
flag: SUCTF{ad1b51464c1b679fe731c7d718af241f}
反调试
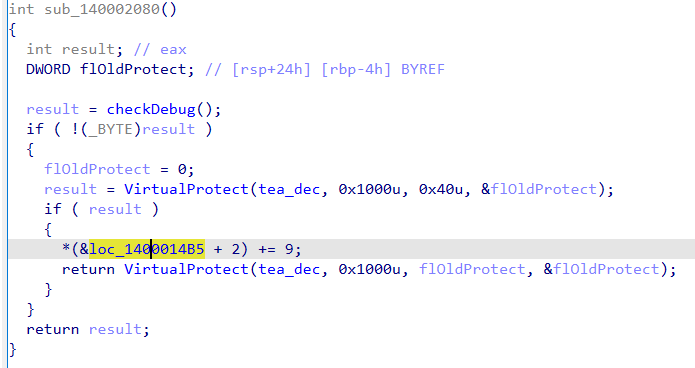
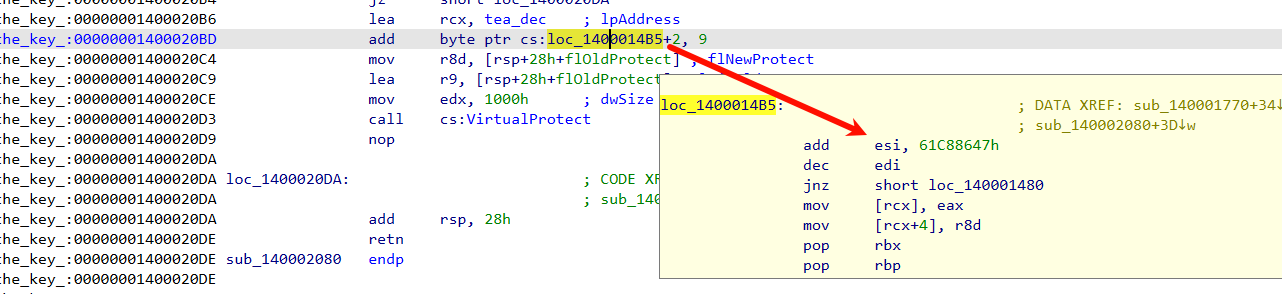
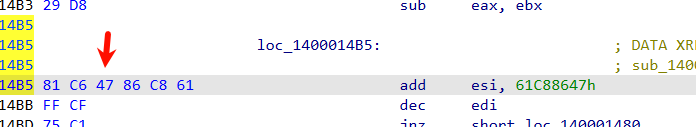
当检测父进程为 explorer.exe 或 cmd.exe 时,对程序进行修补
delta = 0x9E3779B0
Other
1 | struct ranges // sizeof=0x10 |
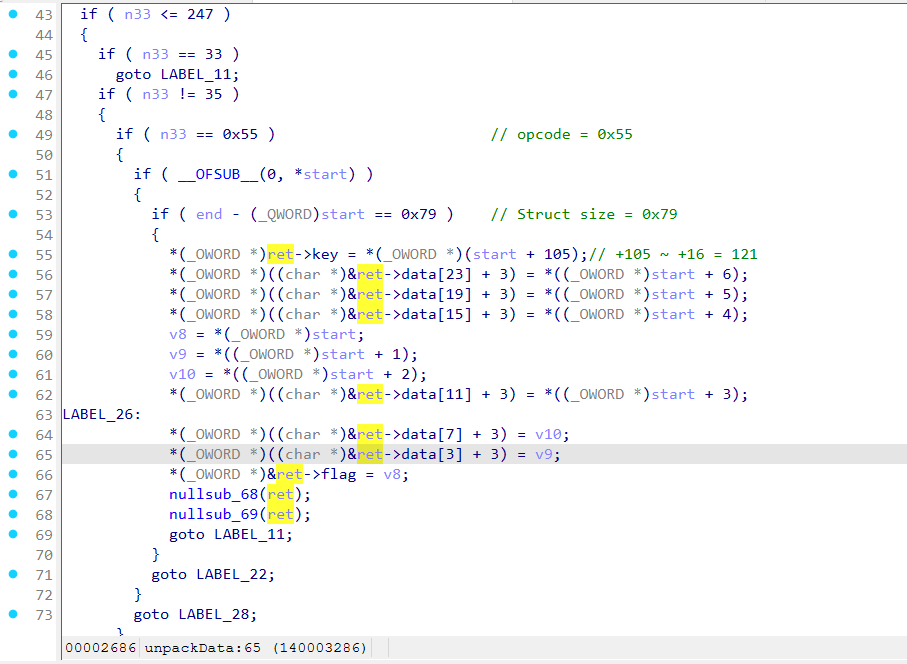
unpackData
编译器做了向量优化,这里可以看出结构体总大小为 121 字节,105 和 23 * 4 + 3 处有部分重合
反序列化
将函数从十六进制字符串转换为 bytes,要求第一个字节为 0x60,然后
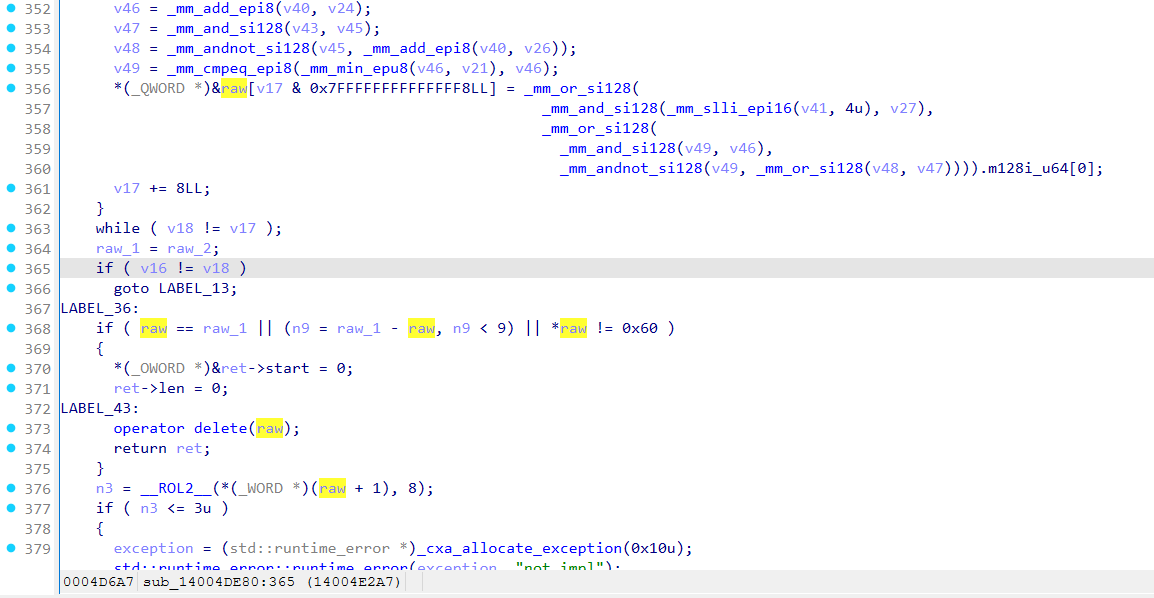
可以看出将 payload 写入结构体
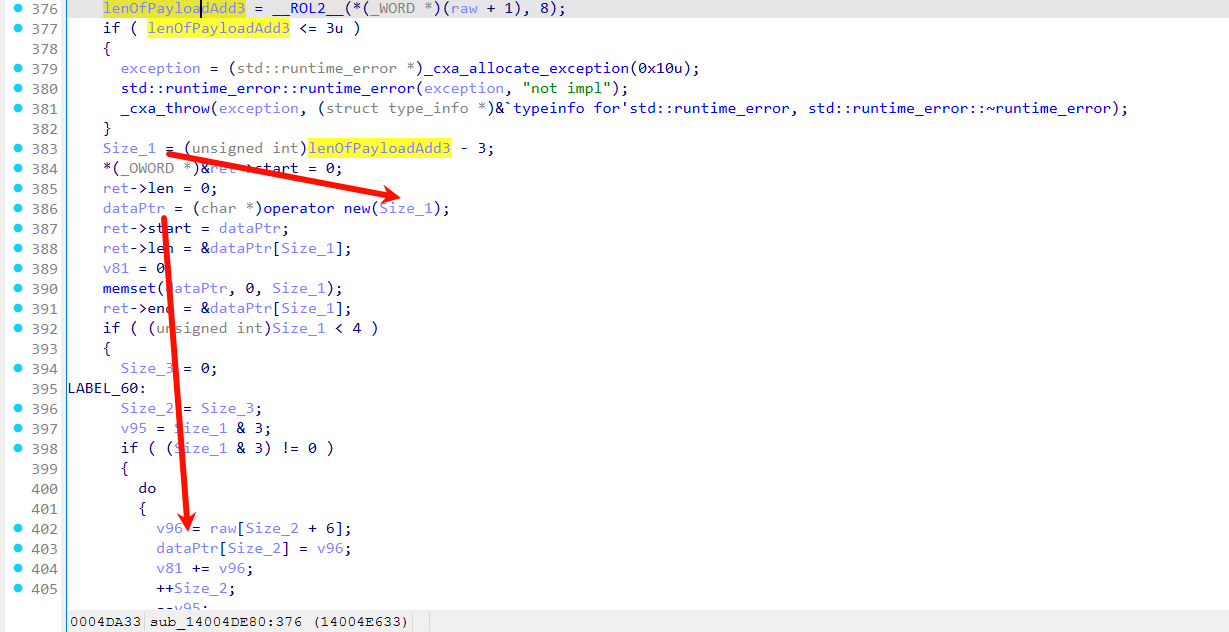
补码计算,约束 opcode = 0x55 走正确的 unpackData 逻辑
版权声明: 本博客所有文章除特别声明外,均采用 CC BY-SA 4.0 许可协议。著作权归作者所有。商业转载请联系作者获得授权,非商业转载请注明出处。
